What sort of data should be considered “private?” Who is responsible for keeping it private? And what happens when that private data is shared or stolen?
As an HR professional, the answers to these questions might be extremely relevant to you. The answers can impact the well-being and productivity of both companies and individuals alike. And while this might surprise you, some of the best safeguards might be offered not by your IT department, but by yours.
In this article, you’ll discover...
Chapter 1: What is data privacy?
Chapter 2: What is Personally Identifiable Information (PII)?
Chapter 3: What can happen when data privacy is breached?
Chapter 4: The costs of identity theft for your employees
Chapter 5: The costs of identity theft for your company
Chapter 6: What are the rules?
Chapter 7: How can identity theft protection help protect data privacy?
Chapter 8: How can you help protect data privacy?
Chapter 9: Why protecting data privacy with an identity theft benefit makes sense
What is data privacy, anyway?
The idea of data protection has been around for a long time. Companies protect the data they store through secure networks, firewalls and a whole range of cybersecurity measures. Who do they protect it from? From hackers, competitors, and anyone else who should not be privy to it.
Determining who should have access to data is the key component of data privacy.
Information that is strictly company-related such as operating data, market research, trade secrets, etc. is usually considered confidential, but the label of “private” is seldom used there. Instead, data is typically labelled as private only when it refers to individualized or personal data.
The idea that private data should remain private and not be shared without consent is what data privacy is all about.
With this in mind, data privacy policies are created by companies to regulate and determine what they should and shouldn’t do with the private data they collect.
But what data should be considered private, you might ask. To answer that, we need to understand the concept of Personally Identifiable Information, or PII.
What is Personally Identifiable Information (PII)?
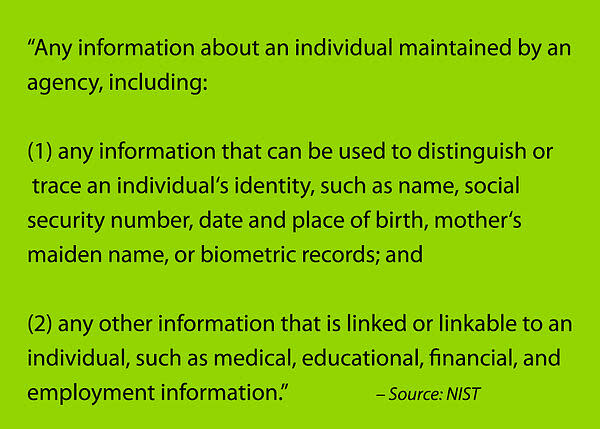
The National Institute of Standards and Technology (NIST) defines PII as:
The list of information that can be directly related to an identity is large. Here are some of the more common ones:
Names. Names are the most obvious form of PII. Luckily, there is enough duplication and similarities between names out there that a full name alone might not identify you completely (unless that name is extremely unusual). Usernames can either be meaningless (as in RobotDuck123) or could help pinpoint your identity by exposing both your name and year of birth (as in JohnSmith87).
Addresses. Taken separately, a street address, town, or state might not provide enough useful details to locate you. But combine them and it becomes very easy to identify a person, just by using public records. Email addresses are important pieces of PII for two reasons:
They provide a single point of access to a person
They often include names and important dates that make it easier to identify a person
Data such as phone numbers, driver’s license numbers, passport numbers, etc. all can be directly linked to an individual and are considered PII.
The problem is that many other pieces of information, some that might not seem like PII, can be used to help identify a person. There are called linkable PII.
Linkable PII includes data such as:
Gender
Race
Age (often just a nonspecific age bracket)
Occupation
And many more. In addition, partial forms of regular PII are considered linkable. For example, a first name without a last name, or a city without a street address, are linkable forms of PII.
PII also includes sensitive data such as medical and financial records. Sometimes these records themselves might provide enough data to identify an individual, while in other cases they are only linkable. Designing databases so that it’s harder to piece those links of data together is one approach companies take to pursue better privacy protection.
The concern with linkable PII is that it often doesn’t take many points to narrow things down to an individual. For example, if all you have is a last name, your chances of finding a person are almost zero. But add a city and an occupation to that, and it becomes much easier.
Because sharing linkable PII data is not as worrisome to most people as sharing, say, their private address or phone number, they tend to expose a lot more of it on the internet. But the problem is that when you start combining pieces of linkable PII, it doesn’t take much to arrive at a unique conclusion… or, in this case, a specific individual.
What can happen when privacy is breached?
When PII is involved in a breach, it can cause many headaches for the individuals involved, up to and including the danger of identity theft.
At the very least, it could mean more linkable PII data exposed to hackers, or posted on the internet or dark web. This could make it easier for identity thieves to piece bits of data together to find a target.
At the worst, full PII disclosure could deliver an easier target to identity thieves, especially when account credentials are breached as well.
Sometimes, a privacy breach occurs simply because linkable PII was not made as secure from external forces such as hackers. Because these data points aren’t considered sensitive, and often seem innocuous and harmless in nature, they might not receive as much in the way of protection.
At other times, PII might be caught in a wide-scale breach involving millions of names, account credentials, and other details.
The problem is that with each new breach, more PII and linkable PII is being made available to cyberthieves through forums such as the dark web. For example, let’s say that one breach attaches medical records to a username, without any other personal identifiers. But a breach at a different company finds that same username, only this time with a name attached. Now the two can be put together.
Privacy breaches can lead to the creation of synthetic identities, where fraudsters use your PII to create a fictitious person. They can lead to being targeted by more traditional online and offline frauds. And they can be used for identity theft.
The cost of identity theft to your employees
When identity theft occurs, it can be devastating for your employees.
They might face incredible stresses in their time, money and relationships.
Regarding time, the average identity theft case takes 100 to 200 hours — or 12 to 25 full workdays — to remedy, according to the Identity Theft Resource Center’s Aftermath studies.
This entire process, from submitting a claim to finalizing paperwork, takes an average of about six months.
Regarding money, the average out-of-pocket costs are $1500. This does not include any funds actually stolen, the amount of which can vary greatly.
Medical record identity thefts, on the other hand, cost an average of $22,346 to resolve.
Regarding relationships, the stress of dealing with identity theft is not the only factor. The hijacking of social media and email accounts can lead to challenging personal and reputational damage. And the financial chaos often brought on by identity theft can lead to struggles in meeting social obligations as well as fiscal ones.
The cost of identity theft to your company
When a privacy breach leads to the identity theft of an employee, it can impact your business, too.
According to Gallup’s State of the American Workplace, employees distracted and stressed over identity theft experience:
70% more employee safety incidents
25–59% higher turnover
17% lower productivity
21% lower profitability
Each of these factors can translate directly to your bottom line. Even one safety incident has the potential to create huge financial disruptions and burdens. As for the rest, when considering a percentage of your workforce rather than a single employee, the results can be troubling.
What is the cost of 100 hours of work? What is the cost of onboarding a new employee?
These are just a few of the more obvious costs companies might be forced to accept when identity theft strikes.
Depending on the industry you’re in, the type of data sought by hackers can vary greatly. Personal data is the #1 type of data targeted in breaches of the financial services and insurance sector and the educational services sector. For most of the other industries, personal data was in the top three.
Here’s an in-depth look at how the costs and risks of identity theft vary by industry.
What are the rules?
What are the rules when it comes to dealing with privacy? The fact that there’s no simple answer is part of the problem.
Companies that do business with the European Union are subject to their General Data Protection Regulation(GDPR). This was passed in 2016 and enforcement of it began on May 25th, 2018. With the goal of giving citizens more control over the use of their personal data, it set some common standards and expectations regarding data protection.
The first large-scale fine for a GDPR violation was recently handed out to British Airways to the tune of $228 million. Many more cases remain in the pipeline, with more hefty fines expected.
In the United States, privacy protection legislation takes a much more piecemeal approach. Many states are enacting their own laws to deal with the issues that keep cropping up in their courts.
In the Pennsylvania Supreme Court, Dittman vs. UPMC set a landmark precedent that companies have an obligation to protect the private data of their employees. When an external hack exposed the private data of 62,000 employees at the University of Pittsburgh Medical Center, the judgment was that they did not adequately protect that data and were therefore responsible.
On the legislation side, the California Consumer Privacy Act (CCPA) is one of the strictest guidelines for companies to follow, and may be the litmus test for compliance once it takes effect in January 2020.
On the federal front, the FTC has been taking close notice of privacy issues for the past several years, but lately has added some teeth to its fines.
In July of 2019, the FTC approved a record $5 billion settlement with Facebook for its handling of users’ private data. Another multimillion dollar settlement was reached with Google that same month for violating the Children’s Online Privacy Protection Act through its YouTube service.
One of the most interesting developments recently was when the Business Roundtable — an association of CEOs from over 200 leading U.S. companies — sent an open letter to Congress, urging them to enact federal data privacy legislation and offering a framework to that effect.
For more detail on data privacy regulations, litigations, and settlements, check out the legal concerns section in How to convince your C-suite to offer identity theft protection.
How can identity theft protection help protect privacy?
Cybersecurity, database design, and organizational controls all play important roles in protecting data privacy. But what about an identity theft protection benefit?
Here are 13 ways an identity protection benefit protects employee data and privacy:
Protects personal data and credentials with a secure wallet
Reduces unwanted solicitations
Informs and advises on current threats
Protects individual employees as well as their families
Monitors the dark web
Provides immediate assistance with call center support
Monitors application submissions
Monitors high-risk identity activities
Monitors credit, debit and checking accounts
Monitors social media
Provides easy credit report access
Freezes or locks credit files
Monitors IP addresses
For a description of how each of these features can help protect data privacy, you can find the explanations in the article linked above.
It’s also important to note the reimbursement strategy of your identity theft protection plan. A good reimbursement plan can give your employees the peace of mind they need when identity theft strikes. So not only can it eliminate their costs, but it can help minimize the stresses and distractions in the workplace, too.
How can you help employees protect their own privacy?
The concept of a digital footprint is used to explain how much data a person “leaves behind” on the internet. Since a digital footprint includes PII data, reducing that footprint’s size is one easy way for an employee to start protecting their privacy.
A few ways to accomplish this are:
Being aware of what you share on social networks, in applications, and via logins
Avoiding unsafe websites
Being careful not to expose your private data on public networks
Deleting accounts and PII sources you don’t need
Staying up to date with software as well as knowledge
Our Beginner’s guide to understanding privacy policies can help your employees browse safer and know what to look for before sharing their information on a site.
And knowing how to set up an application to protect rather than share private data is important, too, especially when so many applications default to a “share everything” status. Creating a super strong password is yet another way to help keep most hackers out of your accounts.
Why protecting data privacy with an identity theft benefit makes sense
Your IT department and its cybersecurity measures are instrumental in keeping all those internal networks and stored data safe. But what happens outside the workplace? If an employee’s PII is compromised on public networks outside of work, it could make it that much easier for hackers to find their way in. In fact, many breaches start in just that way.
That’s why an identity theft benefit makes sense. It can help protect your employees’ privacy and data through all their online journeys, both in and out of work. And not only that, but it can also protect their families, too, leaving even fewer paths for hackers to follow.
Since offering identity theft protection as a benefit relies on enrollment — and, of course, you want as many employees protected as possible — we’ve shared several strategies that can encourage more employees to enroll.
Protecting data privacy is a challenge everyone in your company should embrace. As an HR professional, you can help meet that challenge by offering the resources, tools, and knowledge of an identity theft protection benefit program.


